
Canary Tokens
Generates lightweight, embedded honeypot triggers called canary tokens for detecting unauthorized access.
The software creates lightweight, embedded honeypot triggers—canary tokens—that alert administrators when they are accessed, indicating a possible breach. It runs as a daemon and emulates a variety of network services, so an intruder who interacts with the dummy endpoints generates an alert that includes the source IP and the point of contact. Alerts can be sent through multiple mechanisms configured by the user.
It is written in Python, making it cross‑platform, and can be deployed on minimal hardware such as a Raspberry Pi or a modest virtual machine. The core package is self‑hostable, free, and open‑source under a BSD‑3‑Clause license, with optional modules for protocols like SNMP, Samba, and port‑scan detection that require additional system components. Installation is supported via standard Python tools, Docker, and package managers on Linux and macOS.
The project targets security teams, system administrators, and developers who need a low‑resource, customizable way to detect unauthorized access without relying on external services. Its modular design allows users to extend or modify the honeypot behavior to fit specific environments.
Reviews
Loading reviews…
Similar apps

Email Clients
CanaryMail
Secure email app for Mac and iPhone with built-in PGP Support and AI assistance. ![Freeware][Freeware Icon]
Password & Security
swiftGuard
Tool for protecting USB ports from unauthorized access.

Password & Security
Password Pusher
Dead-simple application to securely communicate passwords (or text) over the web. Passwords automatically expire after a certain number of…
Password & Security
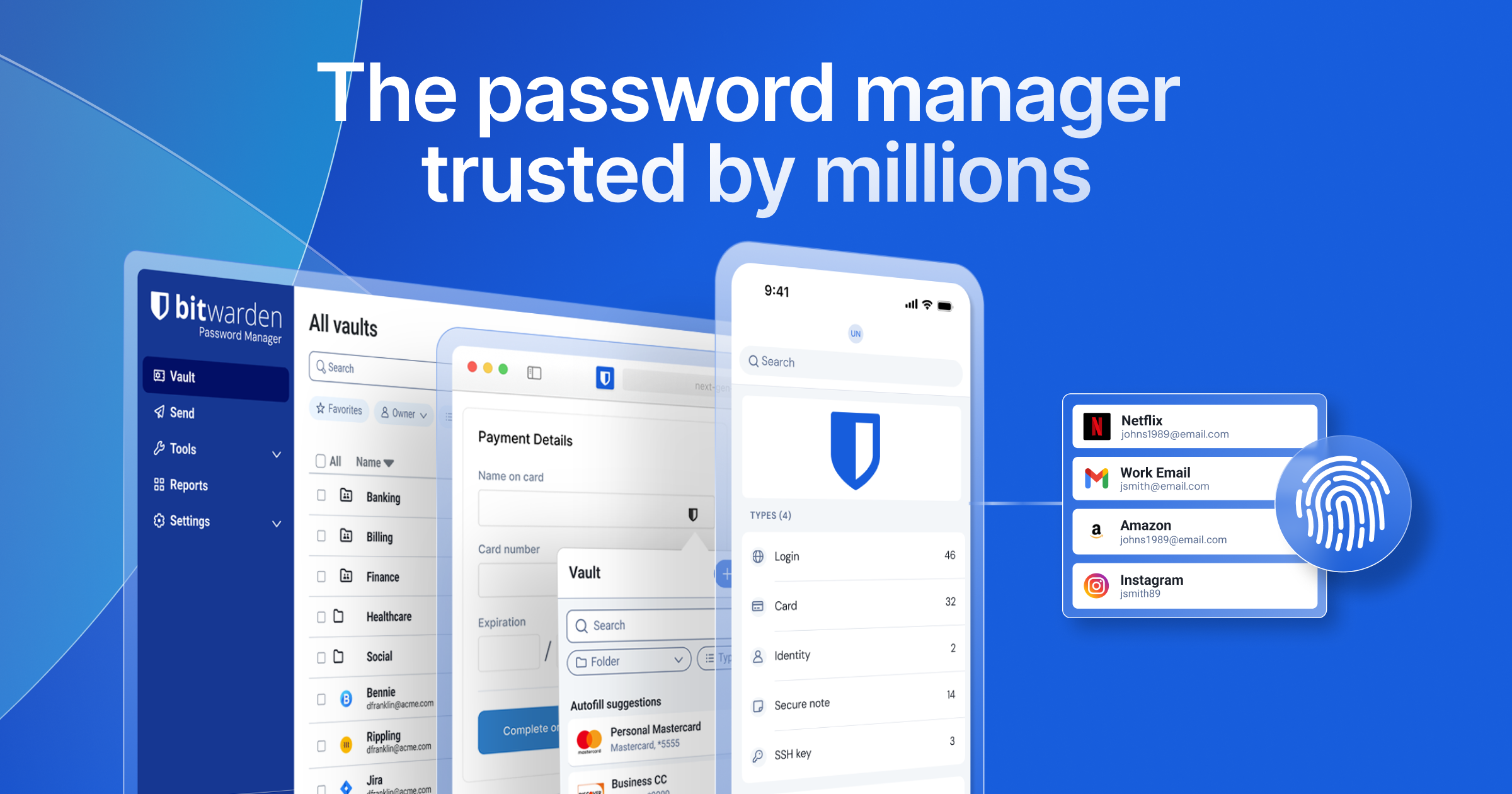
Bitwarden
An open-source password manager with end-to-end encryption, a generous free tier, and clients on every platform.
Password & Security
Hemmelig
Share encrypted secrets cross organizations, or as private persons.
Network & Connectivity
beelzebub
Honeypot framework designed to provide a highly secure environment for detecting and analyzing cyber attacks.
