AWS Vault
Securely stores and accesses AWS credentials in a development environment
AWS Vault stores IAM credentials in the operating system’s secure keystore and generates short‑lived temporary credentials via Amazon STS. It reads profile definitions from the standard `~/.aws/config` file, then supplies the temporary keys to shells or applications either as environment variables or through a subprocess. This approach limits exposure of long‑term keys and integrates with existing AWS CLI workflows.
The tool is aimed at developers and operators who need to work with AWS services from a local environment while keeping secret keys protected. It supports a range of vault backends, including macOS Keychain, Windows Credential Manager, GNOME/KDE keyrings, the Pass password store, and encrypted files, selectable via a flag or environment variable. Users can add credentials, list stored profiles, open a temporary subshell, or launch the AWS console with a single command.
Installation is available through many package managers on macOS, Windows, Linux, FreeBSD, and OpenSUSE, as well as via direct download of releases. Documentation and usage examples are provided in the repository’s USAGE.md file.
Reviews
Loading reviews…
Similar apps
Security & Identity
Cryptr
GUI for Hashicorp's Vault
Security & Identity
Leapp
Cloud credentials manager
Crypto Wallets & Payments
BTCPayServer Vault
App that allows web applications to access a hardware wallet
Password & Security
Gopass UI
Password manager for teams

Version Control & Git
git-secret
Store your private data inside a git repository.
Password & Security
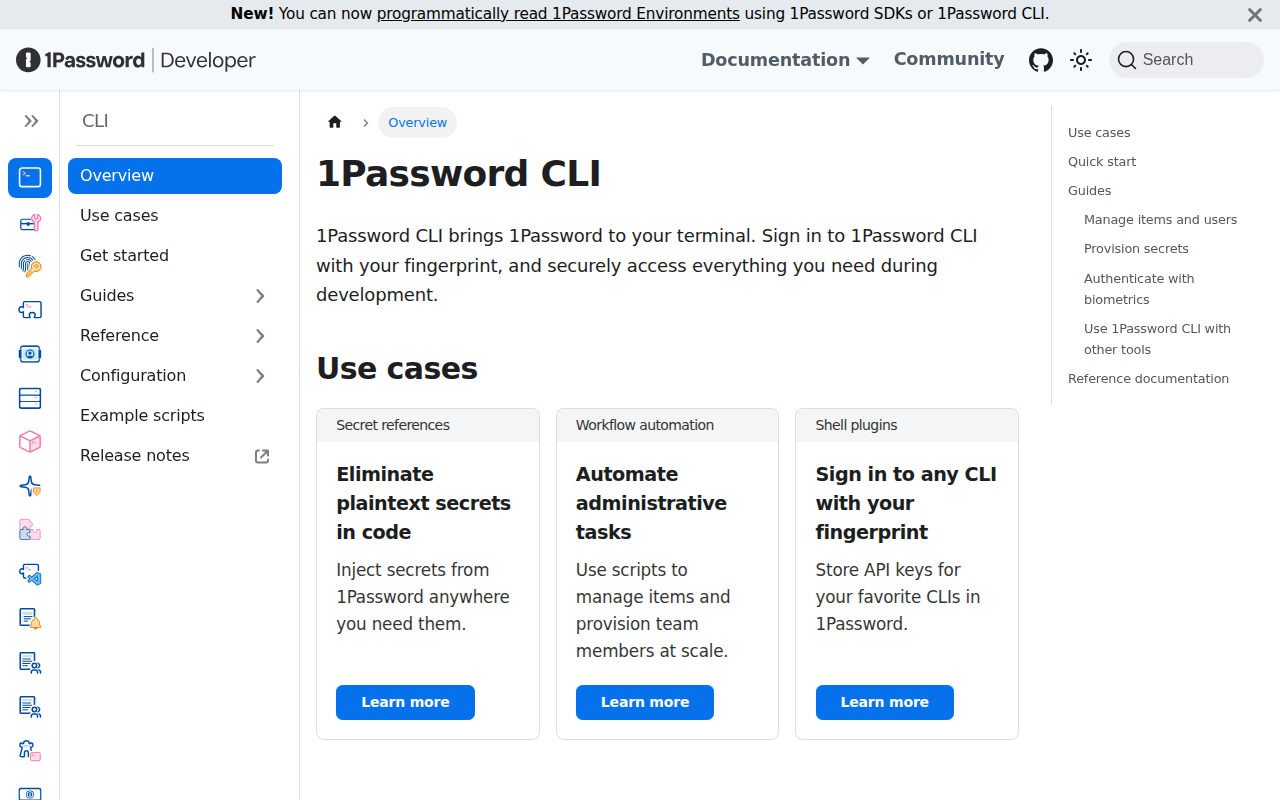
1Password CLI
Command-line interface for 1Password
